ICS/OT Practitioners Share Their Unique Requirements & Concerns
SANS released its annual ‘ State of ICS/OT Cybersecurity’ report in October 2022. It reflects survey results from 332 ICS/OT organizations representing a range of industrial verticals.According to respondents, their 2 nd biggest challenge in securing OT technologies and processes is that “ traditional IT security technologies are not designed for ICS and cause disruption in OT environments.” [1] That certainly applies to Secure Remote Access for ICS/OT, the application for which XONA Systems has created a purpose-built solution
. 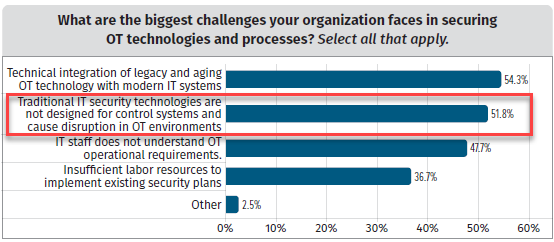
Figure 3. Biggest Challenges in Security OT Technologies and Processes
This viewpoint is not surprising. In February 2022, SANS created an infographic[2] that cited the differences between cybersecurity for ICS/OT and IT environments. It offered guidance on defining the differences between cybersecurity defense methodologies, security controls, safety, impacts, skill sets, and the security missions for ICS/OT versus IT.
One example cited was the (likely) application of a popular remote access and control program named TeamViewer as the vehicle that unidentified cyber actors employed to compromise a U.S. Water Treatment facility. [3] TeamViewer is widely used in traditional IT environments to enable IT personnel to install/update software on a computer where administrative rights are withheld from the end-user out of security concerns.Another challenge, according to SANS, is that “ICS/OT assets are often compared to traditional IT assets; however, traditional IT assets focus on data at rest or data in transit, while ICS/OT systems monitor and manage data that makes real-time changes in the real world with physical inputs and controlled physical actions.” As such, ICS/OT cybersecurity must support the safe operation of critical infrastructure, not the other way around.
Other findings:
- A compromise in IT is the #1 (40.8%) initial attack vector allowing threats into OT/ICS networks.
- Lowering risk/improving security and preventing information leakage are the #1 (53.6%) and #4 (29.1%) OT/ICS business concerns.
- Operator assets, such as a human-machine interface (HMI) or operator workstations, are considered one of the control system components at greatest risk (#2 at 43% - up from 32% in 2021) and one of the control system components with the greatest (negative) impact if compromised and exploited (also #2 at 39.8%).

- Once safety risks and operational impacts from a cyberattack are seen, it’s too late.
References: