There are many significant technology-enabled changes taking place in industrial environments today. Smart factories and Industry 4.0. The Industrial Internet of Things (IIoT). The convergence of information technology (IT) and operational technology (OT). All of these things are introducing digital technologies at a fast pace to improve operations, increase productivity, enhance oversight, and increase profitability.
For all the good the technologies offer, there’s also a dark side that opens up the digital environment to vulnerabilities that can enable cyberattacks, theft of intellectual property, and even cyberwarfare.
The threats and concerns of attacks on industrial systems are clearly evident by the recent Biden Administration and the Cybersecurity and Infrastructure Security Agency (CISA) warning that Russia has been conducting "preparatory activity" for cyberattacks, including scanning websites and hunting for software vulnerabilities, and could attack any critical infrastructure segment in the U.S. The Administration urges owners of critical infrastructure to conduct cyber risk assessments, implement multi-factor authentication, keep software and malware protection up to date and educate employees on the threats. The 62443 standards provide a framework of controls to mitigate the risk of these types of attacks.
It is this deep concern about security vulnerabilities that led several industry regulators to collaborate on the development of a series of standards that create a flexible framework to address and mitigate current and future security vulnerabilities in industrial automation and control systems (IACSs). The main collaborators in this effort are IEC TC65 / WG10, ANSI / ISA-62443, and ISO / IEC-JTC1-SC27. The standards they came up with, known collectively as ISA/IEC 62443, are applicable to all industry sectors and critical infrastructure.
Due to the comprehensive nature of ISA/IEC 62443, the standards are very broad and are presented in 14 separate documents, organized as shown below in Figure 1. They cover a wide range of topics from terminology, concepts, and models to security technologies for IACS, and much more. The standards are written for various audiences, including plant operators, integration and maintenance service providers, and component/system manufacturers.
In terms of the broad aspects of the standards, XONA provides capabilities for security requirements in the three areas highlighted in green, below.
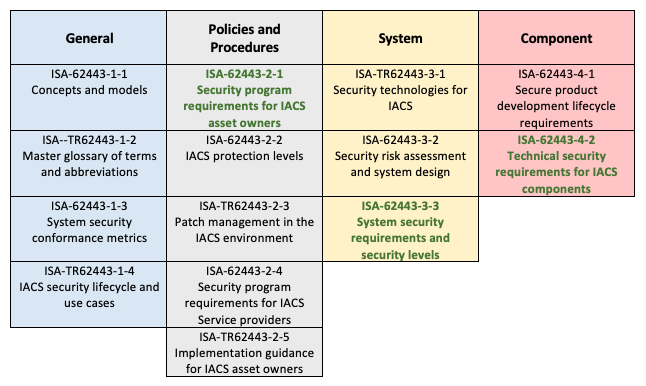
Figure 1 – Documents for ISA/IEC 62443
Trust us when we say the standards are very broad and deep. It took us weeks to scrutinize every requirement to determine if, and how, XONA supports the standards. The truth is, no single component or system manufacturer can claim to cover every single requirement—the needs are just too diverse. The standards were written to go across multiple technology providers, which explains why system integrators are one of the target audiences of the document: someone needs to put the diverse pieces together to help a company achieve full coverage.
Practitioners and customers often ask if we “comply” with ISA/IEC 62443. This is a bit of a misnomer, as 62443 is not a regulation mandated by a government or industry agency, such as NERC-CIP is for the energy industry. Instead, 62443 is a set of recommended standards that can help companies with industrial automation and control systems protect and secure those systems. Our customers seek to confirm compliance as they have adopted 62443 as a corporately mandated cyber security standard That said, XONA security capabilities and features meet the foundational and security level requirements of the relevant 62443 standards and fulfill the compliance requirement.
Meeting ISA/IEC 62443 Standards
Leading industrial organizations worldwide trust XONA for secure user access and analytics for their critical systems. XONA provides granular user-to-asset access controls and user session analytics via a zero-trust architecture. By integrating with OT asset management and security information and event management (SIEM) platforms, XONA adds the essential user-to-asset access control and analytics components needed in industrial infrastructure today.
Given these capabilities, it’s a natural fit for XONA to address various aspects of 62443, specifically around access control, identification and authentication control, use control, data confidentiality, and least privilege. These fall within XONA’s functionality and areas of expertise for securing industrial networks and systems. An important consideration is to select technology that aids in meeting and staying compliant and not undo any security countermeasures.
Because of the complex and detailed nature of these requirements, we've created a datasheet that explains which of the requirements XONA meets and how. Download it now:
If you’d like to discuss how we fulfill those requirements and can help your organization improve user access control, schedule a demo today.





























