And Xona Can Help You Take Back Control of Your User Access for Critical Infrastructure in Under 1 Hour!
Introduction – Why Controlling User Access to Critical Systems is So Crucial
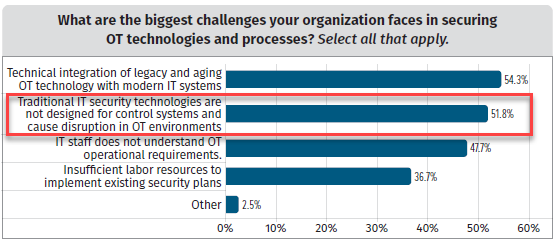
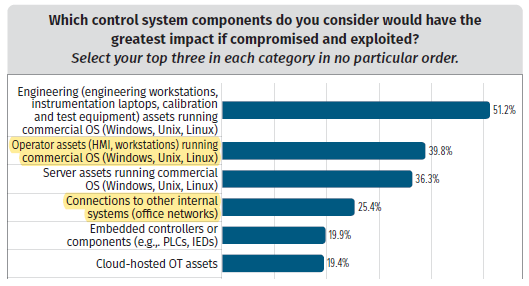
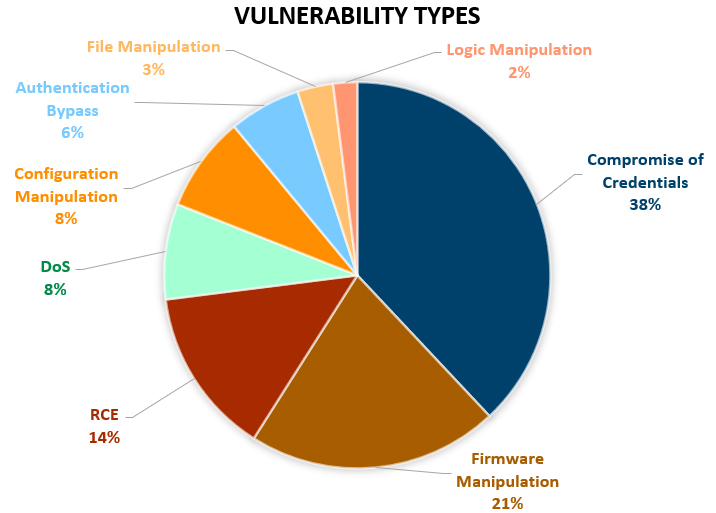
In today’s rapidly evolving threat landscape, user access control is the single most important, foundational cybersecurity priority for critical infrastructure owners and operators. Attackers continue to exploit weaknesses including legacy remote access mechanisms, and the consequences are severe. A few indicative statistics of this priority include:
Remote services were the primary attack vector in 71% of major cyber-attacks on OT environments.1
Ninety one percent (91%) of security professionals express concerns about VPNs compromising IT security.2
These statistics highlight a harsh reality—outdated access solutions like VPNs and jump servers are no longer sufficient to protect critical infrastructure. Attackers exploit gaps in identity verification, authentication, session controls, and open network access, leading to ransomware, system breaches, and operational downtime.
Organizations that lack centralized control over user access expose themselves to increased cyber risk, regulatory penalties, and inefficiencies that threaten operations. The solution? A modern, purpose-built critical infrastructure approach to secure access.
This blog explores what it truly means to take control of user access, outlines the key steps, and explains why Xona is the obvious choice in secure access for critical infrastructure.
What Does It Mean to Control User Access?
Taking control of user access means moving beyond legacy, fragmented access solutions and implementing a centralized, identity-based approach designed specifically for critical infrastructure environments. Without full control, organizations remain vulnerable to unauthorized access, operational inefficiencies, and regulatory penalties.
Before and After: The Risks of Poor Access Control
Before Xona Organizations relying on legacy access methods–face persistent cybersecurity risks, with broad attack surfaces and limited oversight of remote sessions. | After Xona A unified, identity-driven access model ensuring only authorized users can access critical systems, with complete auditability and session control. |
| Scattered & Unsecure Access: Remote users, vendors, and third-party contractors use multiple access methods (VPNs, jump servers, RDP, SSH), creating security gaps. | Centralized & Secure Access: Xona provides a single, browser-based access platform with zero trust security, eliminating risky direct connections. |
| VPN Complexity & Vulnerabilities: VPNs provide broad network access, increasing attack surfaces and compliance risks. | VPN-Free Secure Access: Xona removes VPN dependencies, enforcing granular access control with least-privilege principles. |
| OT & IT Silos: OT teams lack a streamlined, secure way to access ICS and industrial systems without IT-heavy tools. | Seamless OT & IT Integration: Xona bridges IT and OT with identity-based access that works with existing IAM and PAM solutions. |
| Compliance Nightmares: Meeting NERC-CIP, IEC 62443, TSA SD2, and other mandates is resource-intensive and difficult to prove. | Built-in Compliance & Auditability: Xona simplifies compliance with automatic session recording, access logs, and audit-ready reports. |
| Operational Bottlenecks: Secure remote access is slow, requiring IT approvals and complicated login processes, delaying troubleshooting and maintenance. | Fast & Effortless Access: Xona enables users to connect in seconds, reducing downtime and improving operational efficiency. |
| Risky Third-Party Access: Vendors and contractors often have excessive, uncontrolled access, leading to potential insider threats. | Controlled Third-Party Access: Granular, time-limited, and monitored sessions ensure vendors only access what they need, when they need it. |
| Unmonitored User Sessions: No visibility into who accessed what and what was changed during the session, making security incidents difficult to investigate. | Full Session Visibility & Oversight: Xona provides real-time session monitoring, video recording, and administrative override controls. |
| High Admin Overhead: Multiple solutions and components stitched together increases admin overhead and maintenance requiring management of multiple access solutions and constant patching and troubleshooting. | Simple & Low-Maintenance: Xona’s zero-client, agentless platform reduces admin workload with fast deployment and minimal ongoing management. |
Key Steps to Taking Control of User Access to Your Critical Systems
Securing critical infrastructure requires a comprehensive, zero-trust approach that prioritizes identity, enforcement, visibility, and compliance. Below are the essential steps organizations must take to eliminate security gaps and establish a resilient user access framework.
- Universal User Access Platform, Purpose-Built for Critical Infrastructure
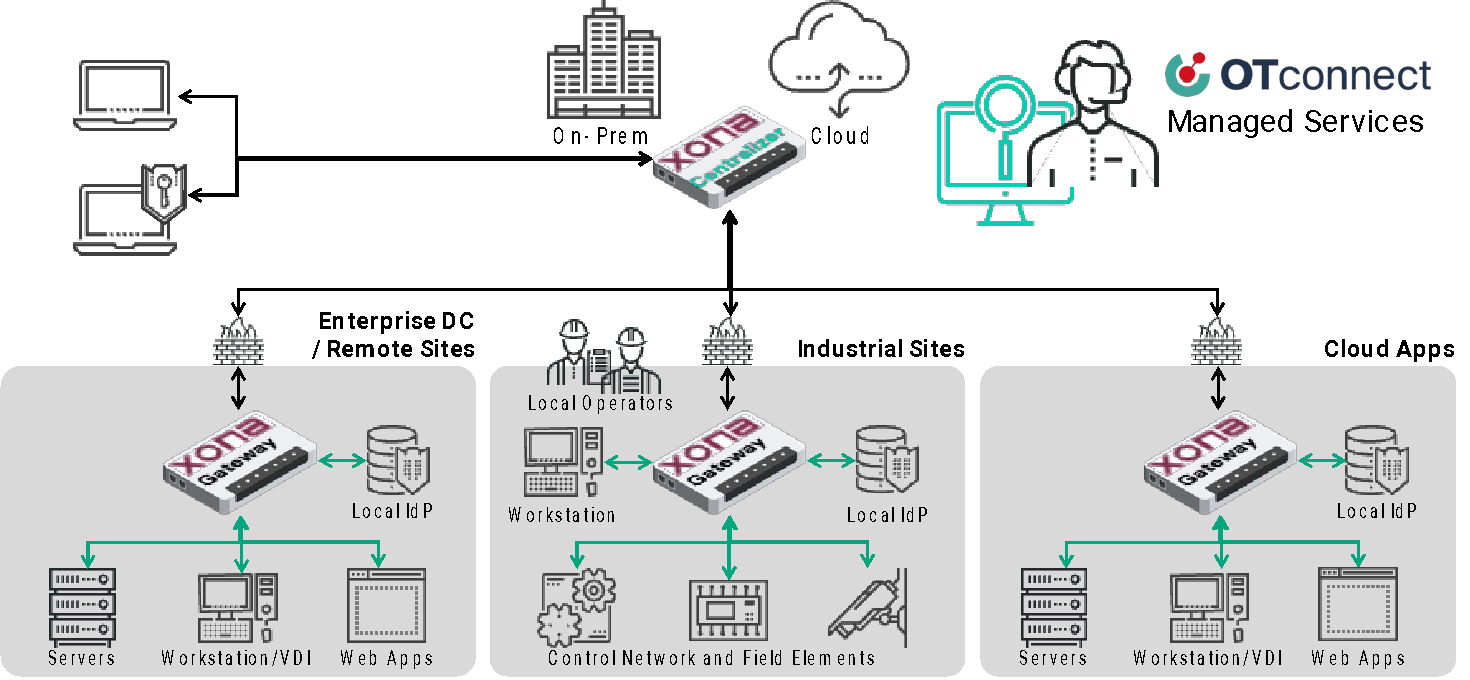
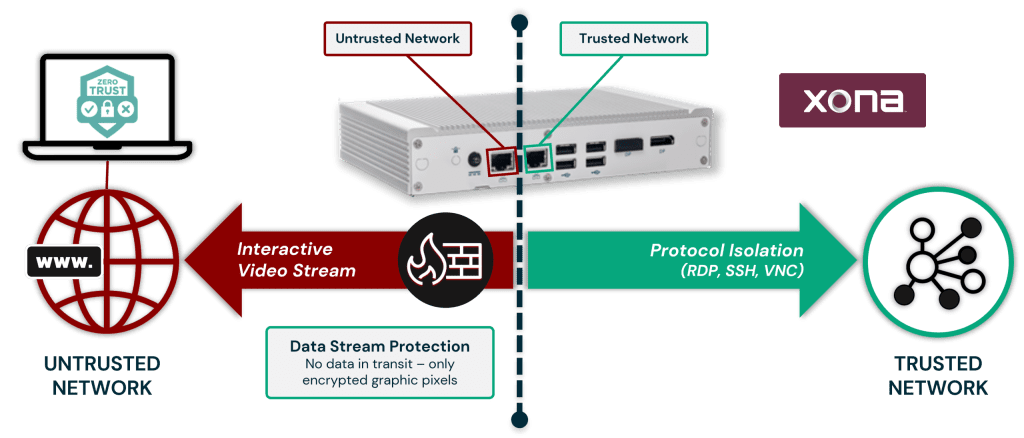
Legacy IT-based solutions fail to meet the unique needs of OT environments. Xona’s platform is designed specifically for critical infrastructure operations, ensuring seamless, scalable, and secure access for internal employees, remote users, third-party vendors, and OEM partners. - Standardized Identity Administration, Authorization, Authentication, and Policy Enforcement
Fragmented identity systems create blind spots and compliance risks. A centralized approach to identity management ensures consistent enforcement of access policies, supporting Active Directory (AD), LDAP, SAML, MFA, IAM, and PAM integrations for IT and OT convergence. - Enforcing Least Privilege and Zero-Trust Access
Persistent access increases attack surfaces and business risks. Implementing just-in-time access and role-based access control ensures that users only access what they need, when they need it, reducing insider threats and unauthorized privilege escalation. - User Session Supervision, Collaboration, and Override
Security and operations teams must have real-time oversight into user activity. Xona’s platform enables continuous session monitoring, collaborative troubleshooting, and immediate administrative override when necessary to prevent misuse or unauthorized changes. - Delivers on Compliance Mandates
Regulatory frameworks such as NERC CIP, IEC 62443, TSA Security Directives, and NIST 800-53 demand strict access controls and auditability. Xona’s solution simplifies compliance by enforcing granular access controls, full session recording, and capturing detailed session logs. - Simple to Deploy, Administer, and Use
Traditional remote access solutions are complex and time-consuming to implement. Xona eliminates network reconfigurations, agents, and additional infrastructure, providing a frictionless, browser-based user experience that’s technology agnostic and easy for administrators and end-users alike.
By following these key steps, organizations can take back control of user access, reduce their attack surface, enhance compliance, and strengthen overall security while ensuring seamless, uninterrupted operations.
Why Xona? The Best Secure Access Platform for Critical Infrastructure
When it comes to taking back control of user access, Xona is the clear leader. Why? Because Xona provides the simplest, fastest, and most secure way to manage user access across critical infrastructure.
1. Take Control in Under One Hour
Unlike traditional solutions that take weeks or months to configure, Xona can be fully deployed in under an hour.
- No network reconfigurations, no user agents, no cloud dependencies.
- Eliminates the need for VPNs, jump hosts, and complex firewall rules.
- Deployable as on-prem hardware (1U, DIN rail) or virtual appliances.
- Integrates seamlessly with existing identity systems (AD, LDAP, SAML, MFA, PAM).
- Frictionless browser-based access with minimal training required.
2. Purpose-Built for Critical Infrastructure
Xona was designed from the ground up for operational technology (OT) environments, ensuring it meets the unique challenges of securing industrial networks.
- Zero-trust architecture that enforces least-privilege access.
- Real-time monitoring and session controls to ensure continuous oversight.
- Seamless identity federation between IT and OT systems for unified access control.
3. Simple to Administer and Use
Security solutions shouldn’t slow operations down. Xona simplifies access management while maintaining the highest level of security.
- Eliminates the need for complex VPN or jump server management.
- Supports just-in-time access controls for third-party vendors.
- Enables centralized identity management across multiple domains.
4. Compliance-Ready from Day One
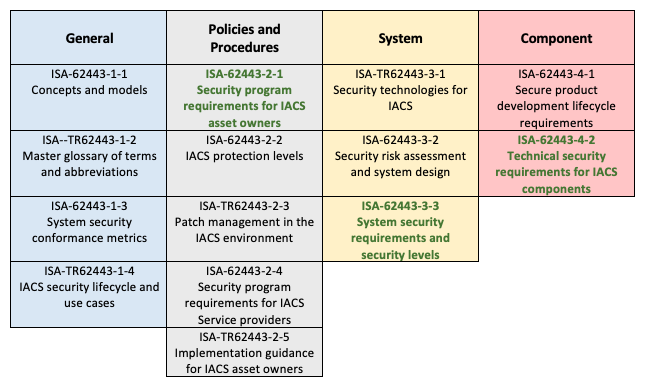
Xona’s platform is built to help organizations meet strict regulatory requirements such as:
- NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection)
- IEC 62443 (International standards for industrial cybersecurity)
- TSA Security Directives for pipeline and rail cybersecurity
- NIST 800-53 for federal IT security standards
With Xona’s pre-configured compliance controls, organizations can ensure secure access without additional customization or infrastructure changes.
The Bottom Line
Taking control of user access shouldn’t be complex or time-consuming. With Xona, you can secure critical infrastructure in under an hour, simplify access management, and eliminate the risks of legacy remote access solutions.
Ready to see how it works? Request a demo today and take control of user access before it’s too late.
Endnotes
- New Study Reveals 92% of Industrial Sites at Risk from Unsecured Remote Access, Takepoint Research, 2024.
- ThreatLabz 2024 VPN Risk Report, Zscaler.